Hello Mythos
In today’s rapidly evolving technology landscape, the building blocks of intelligence, particularly LLMs, are changing every three to six months. In that environment, cyber defence cannot be hard wired to a handful of models. It must be agile, adaptive, and architecture agnostic.
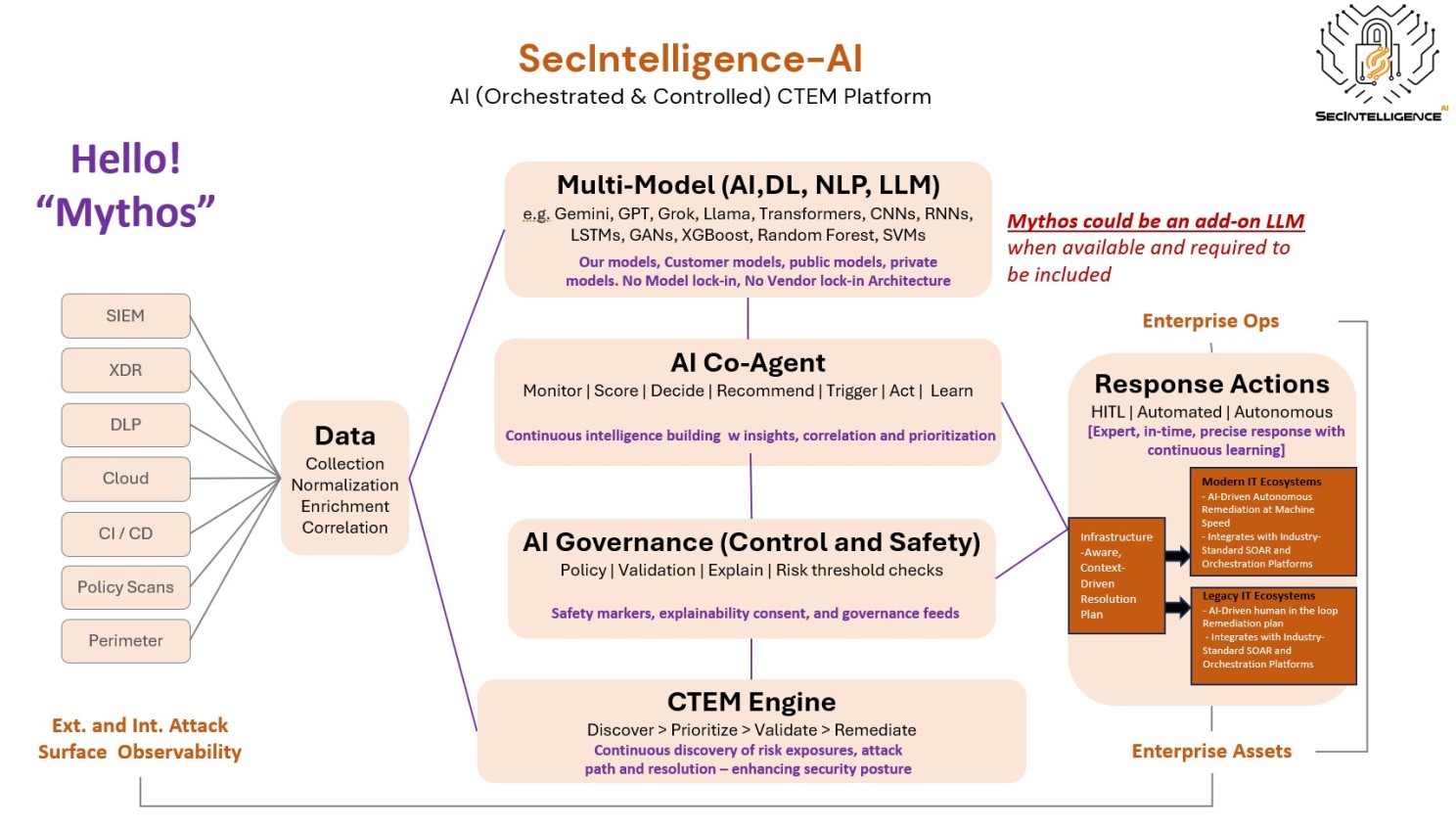
SecIntelligence AI is built exactly that way.
The Threat Is Accelerating
When Mythos reaches general availability, adversaries will move faster than any human response cycle can match:
- Polymorphic malware generated at scale
- Attack paths discovered faster than scanners can map them
- Recon and exploit chaining fully automated
The battleground is shifting. Detection precision matters less. The quality of your decisions and the speed of your control become everything.
How SecIntelligence AI Leverages Mythos
Mythos is not just another model. It represents a steep change in deep reasoning. SecIntelligence AI puts that to work:
- Semantic pathfinding: reasoning across exposures and attack paths rather than simply linking components
- Adversarial pre-emption: thinking like attackers before they act
- Controlled lab simulation: if Mythos can find an attack path, we find it first and harden proactively
Safeguarding Against Adversaries Using Mythos
Attackers will use Mythos for autonomous exploit chaining and sophisticated social engineering. But their motives do not change. Credential theft, lateral movement, and malware deployment remain constant.
Mythos generated payloads also leave traces. Machine generated code, phishing, and attack patterns carry detectable signatures. SecIntelligence AI detectors are purpose built to flag AI generated malicious patterns and neutralize them immediately.
The SecIntelligence AI Difference: AI Orchestrated CTEM Platform
Our AI orchestrated CTEM platform is not just using AI. It is controlling it.
It is built on a multi model abstraction layer. Mythos integrates like any other LLM without creating vendor lock in. We adopt best of breed models as they emerge.
What makes this safe is our AI Control Plane, built on three pillars. A Policy Enforcement Layer ensures every AI action operates within defined boundaries. Risk Thresholds are sourced directly from real exposure data, not probabilistic guesswork.
CTEM validates reality. LLMs can hallucinate. Our decisions are grounded in actual exposure data, always.
We also run Continuous Feedback and Guardrails:
- Reinforcement learning from real outcomes
- Attack simulation validation in shadow environments
- Continuous AI drift detection
The Bottom Line
Mythos will be widely adopted by defenders and attackers alike. The winning strategy is not who uses it. It is who controls, validates, and secures it.
SecIntelligence does not let AI operate unchecked. Every decision is explainable. Every action is auditable. Every AI output is validated before execution.
We assume attackers use AI. We build for it. And we govern it.